Devo Technology Previews Next-Gen Cloud SIEM, Modern SecOps
Devo Technology has released a tech preview for a new-gen SIEM built from the ground up for the cloud era. Devo Security Operations combines machine learning, automation, and cloud-scale.
Devo Technology has released a tech preview for a new-gen Security Information and Event Management solution designed from the ground up for the cloud era.
With its Devo Security Operations preview, the company looks to demonstrate how machine learning, automation, and cloud-scale can push SIEM to the next level of responsiveness and proactive intelligence.
Devo’s goal is to deliver “next-gen SIEM” and move SIEM beyond alert management to provide a smart, all-seeing central hub for data and processes. With faster and deeper access to data from all across the enterprise, security operations professionals can be better equipped to mediate against growing threats, according to Devo’s Julian Waits, general manager of the firm’s cyber security unit.
The release of the Devo Security Operations preview comes as three significant trends are putting straining the ability of a traditional SIEM approach to provide the tools and insights needed by the Security Operations Center (SOC). Among the, Devo execs list these:
(1) an explosion in variety, velocity and volume of data
(2) an expansion of attack surfaces – across on-prem, hybrid, cloud and even multi-cloud enterprise environments and
(3) modern attacks and adversaries are getting more sophisticated
“The effectiveness of the SOC and cybersecurity as a whole comes down to the effectiveness of security analysts. It is quite obvious that legacy SIEMs fail to provide the visibility, insight, and workflows required to support the modern analyst,” Waits said in a statement. Many traditional SIEM solutions are cracking under the strain. The size, scope and opacity of attacks continue to grow, just as the window of time to respond is shrinking. This often leads to strain – of analysts, data scientists and technology, he added.
To counter this increasingly hazardous environment, Devo execs say it’s time to update traditional SIEM solutions. In specific, the Devo Security Operations preview looks to push SIEM beyond its traditional alert management functions to provides a “central hub” for all data and processes, Waits noted.
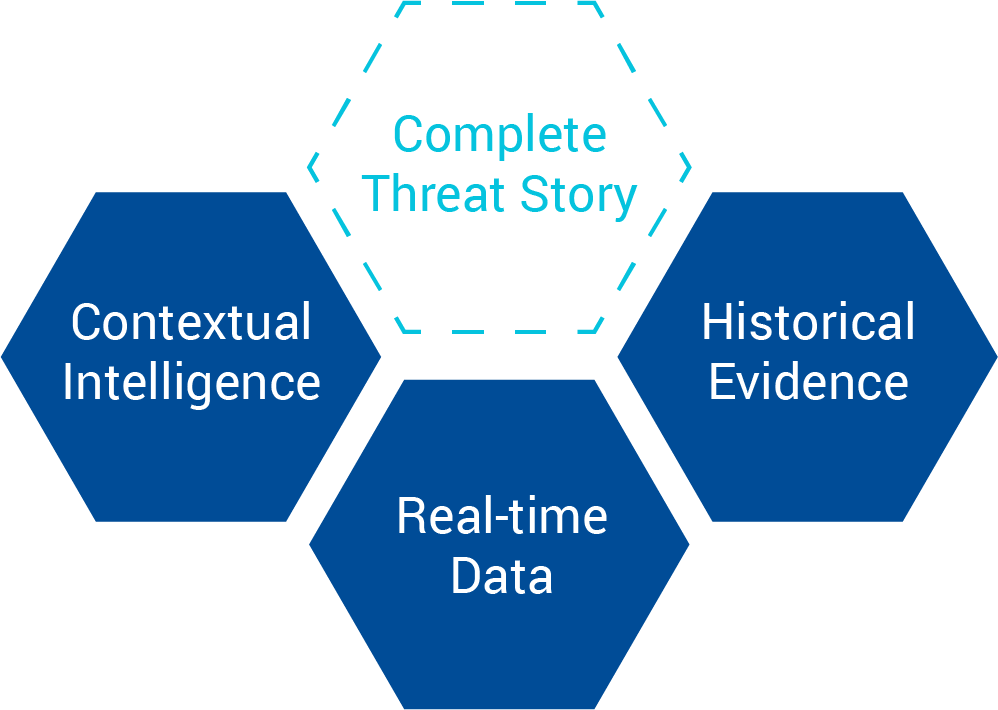
Such an approach would let SOC analysts collect, store, and analyze any data type from any source with ease quicker and deeper. Such access to meaningful data would produce a much faster response and more innovation to detect and deter threats. “With greater visibility, analysts can focus on high impact threats, magnify analyst intuition, and improve the speed and accuracy of triage, investigation, and response,” the company said.
Further, data scientists would gain more control to use ML to develop and deploy models.
Inside the Devo Security Operations – Capabilities and Approach
Devo Security Operations aims to deliver a next-gen cloud SIEM that provides more visibility, clarity and control for the latest chapter of the battle against cyberthreats. Among the benefits that Devo’s cloud-based SIEM aim to deliver include:
Collaborative analysis Devo Security Operations allows SOCs to conduct “collaborative analysis” to make threat investigation faster and more efficient. Devo also provides access to a community of incident response experts. You can choose to engage with Devo customers, peers, and providers across the global community, or share across different regions within your own company.
Rapid, Automated Data Enrichment, Analysis: To further aid SOC analysis, Devo embeds capabilities to automatically enrich data at scale via open, proprietary and commercial threat intelligence sources. This lets SOC teams more rapidly complete intelligent analysis.
Analytics for new workloads: The Devo platform responds to hundreds of thousands of queries simultaneously, in real time, with zero latency. All analytics are made available via our APIs to support your automation and other third-party tools.
Enable SOC analysts to view past and present simultaneously: In contrast to a traditional SIEM platform approach to data, where there are ‘silos’ of cold, warm and hot data, all data in Devo is ‘hot.’ This lets analysts to seamlessly analyze real-time data streams alongside years of historical data. Query PBs of data in a flash with Devo micro-indexing technology and compression, while keeping storage to a minimum.
Sets a foundation for machine learning to act on: Operations teams get out-of-the-box ML while data scientists gain the ability to customize. With Devo Time Series Anomaly Detection, monitor thousands of metrics. The Devo ML Workbench lets you deploy custom models and run them against massive amounts of streaming and historical data.
More straight-forward, seamless ways to combine and enrich data: Users can enrich and combine 100% of their machine data to obtain deeper context. By eliminating traditional indexes, Devo goes beyond isolated views by storing all data together in its raw form. This promotes easy ways to add new sources and join and enrich any data type – all in real time.
The Power of a Cloud-Native SIEM
Devo execs claim next-gen SIEM must be cloud-based. The Devo website describes it this way: “SIEM must be cloud-native, combining SaaS-based services with core product capabilities, and offer flexible deployment models that enable enterprises and MSSPs to streamline security operations as they shift to the cloud.”
Devo also has other suggestions for this next-gen SIEM, including:
Behavioral analytics: SIEM must make ML-based behavioral observations of users and systems on the network the foundation of detection; this will enable analysts to move beyond restrictive rules-based detection to reliably identify high-impact threats.
Community collaboration: SIEM must foster a community among peers by operationalizing threat sharing of curated proprietary, open, and commercial intelligence, and providing access to a community of global CERTs.
Analyst insight: SIEM must capture and learn from analyst behavior to help automate investigations, improve decision-making, and speed onboarding of new security talent.
Orchestration & automation: SIEM must enable rapid threat response through integration with solutions that automate manual, repetitive processes, and orchestrate the incident-response workflow.
In a recent blog post, Devo’s Chris O'Brien, director of technical marketing, described how a deeper focus on data integration and data alignment at the platform level will modernize SIEM activities – and improve responsiveness.
Technology is changing faster than ever; enterprises add new machine data sources all the time, and it becomes cumbersome to stand up and manage new point product solutions to gain full visibility. What’s more, a better understanding of environments is difficult to achieve with so many disparate tools – IT professionals would need to constantly be trained on these solutions, again creating more silos. With this knowledge in mind, it’s even more important to build using a scalable, source-agnostic tool.
Logs and metrics are too important to be independent of each other. The DevOps culture is built on the premise that the critical information they provide will be used to maintain continuous delivery, keeping applications running smoothly and users happy. When logs and metrics are integrated into a single ELM solution, it not only simplifies environmental complexities, but allows businesses to move beyond the constraints of slow data silos and to operationalize all their machine data.
Explore the Devo Security Operations preview here. https://www.devo.com/






