Centrify Analytics Service Uses Machine Learning and User Behavior To Stop Breaches in Real Time
A Forrester Research study, commissioned by security firm Centrify, estimates 1 billion identities were compromised in 2016. The firm is also launching Centrify Analytics Service to shore up access protection with real-time analytics and machine learning.
Building security policy for employees, contractors, partners and privileged IT users has typically favored security over user experience. And yet, a Forrester Research study revealed the enterprise security industry is failing, with organizations being breached at an alarming rate.
The Forrester study, commissioned by security solutions firm Centrify, is titled Stop the Breach: Reduce the Likelihood of an Attack Through an IAM Maturity Mode. It found two-thirds of organizations reported five security breaches in the past two year, on average. The study also estimated more than one billion identities were compromised by hackers in 2016 alone.
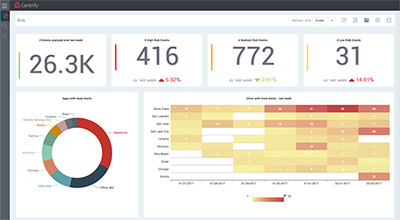
To fill in the gap for protecting data from unauthorized access, the company is launching its Centrify Analytics Service, which aims to stop cyberattacks that lead to data breaches through the use of behavior-based scoring, according to Centrify’s chief product officer Bill Mann.
“Behavior-based scoring means users get a frictionless experience when they present low risk, easing access and improving productivity - while maintaining high security,” Mann said in a statement.
To develop these scores, the Centrify Analytics Service uses machine learning to assess risk based on user behavior patterns over time. From this data gathering, the service then assigns a risk score, determines whether user access is granted (or not) and even enforces on-going access governance - determining whether to give the user direct access based on current credentials, to require step-up (or multi-factor) authentication - or to block access entirely, he added.
“By tailoring security policy to each individual’s behavior and automatically flagging risky behavior, we’re helping IT professionals minimize the risk of being breached - with immediate visibility into account risk, without poring over millions of log files and massive amounts of historical data,” Mann added.
Further, Centrify Analytics Service is designed to protect a broad array of enforcement points across the enterprise -- endpoints, applications and IT infrastructure. “We can enforce risk-based policy in real time, at the point of access. This means high-risk threats can be blocked, while low-risk users get authorized access to apps, privileged credentials, or privileged sessions,” Mann added.
Centrify’s Analytics Service approach looks to several factors to deliver its risk-based scoring approach to access management, Examples include:
- Single sign-on (SSO) to applications: As long as end-user’s behavior is in keeping with typical access, it presents low risk, and IT can provide easy one-click access to their apps.
- Multi-factor Authentication (MFA) for password checkout: When an IT admin checks out a privileged credential or initiates a privileged session to a server or other resource from a location that’s not typical, the risk level is elevated, and the admin is prompted for further authentication.
- MFA for outsourced IT: If an attacker attempts to leverage an outsourced IT credential from an unknown or previously unseen device, access can be blocked entirely, stopping the attack before it can gain traction.
The Centrify Analytics Service is part of the company’s Centrify Identity Services Platform and is available as an add-on to Centrify Identity Service and Centrify Privilege Service.
Readers can learn more about Centrify’s Analytics Service or start a trial on the Centrify solutions site.
Forrester / Centrify Security Survey Shows ‘Trust’ at Risk – Not Just Data
To Centrify’s CEO Tom Kemp, the Forrester survey highlights how important it is to pay attention to growing vulnerabilities of the digital business.
For years now, Kemp noted that organizations have relied on a well-defined boundary, supported by digital walls and gatekeepers, to protect their assets. “But today, with the rapid introduction of new technologies, platforms, applications and practices, that border has disintegrated, resulting in significant exposure for the global enterprise,” he added.
So, in response to today’s hybrid and cloud architectures, companies need to be empowered to more quickly diagnose and implement solutions, according to Kemp. In the balance is not only a company’s valuable data, but the arguably more valuable trust it enjoys with customers and employees, he argued.
Kemp put it this way in a recent blog post:
I don’t think we can overstate the impact of what a complete loss of trust would mean to our future. Without trust, how can we continue to use the technologies we have, much less adopt new ones? With the current state of security, would we ever be able to climb into an internet-connected, self-driving vehicle with any level of confidence?
The Forrester survey includes responses from more than 200 enterprise IT security decision-makers in charge of identity and access management. It highlights the need for better approaches, when it pointed out that despite spending $75B on security in 2016, 83 percent of organizations are at high risk.
Kemp laid out why identity is a key focus of the survey, saying “Identities live in and out of the enterprise, creating a new dimension in security. Most accessed by one simple permission: the password.”
Other notable highlights from the survey results include:
Organizations with the highest IAM maturity experience half the number of breaches as the least mature. For instance, they are 46 percent less likely to suffer a server or application breach, 51 percent less likely to suffer a database breach and 63 percent less likely to suffer cloud infrastructure breach.
Organizations that secure both regular and privileged access are less likely to experience a breach compared to those organizations that adopt fewer best practices. Forrester estimates that 80 percent of security breaches involve privileged credentials that typically belong to the IT professionals who administer the systems, databases and networks of an organization.
Organizations with the least IAM maturity averaged over 12 breaches, more than twice the number of breaches of the most mature, and endure more than $5 million more in financial damage.
Mature companies spend more on overall IT security versus the least mature companies, but actually spend less on IAM technology as a percentage of their entire budget—40 percent less. This translates into an additional cost savings of $2,582,000, which not only makes these organizations more capital efficient, but also allows them to better streamline their IT infrastructure by eliminating redundant IAM technologies.
The study’s conclusion: A “maturity hierarchy” exists in the marketplace. The most mature groups employ more IAM, as well as use integrated IAM technology platforms rather than multiple point solutions, to reduce security risk and may avoid millions in data breach costs over their less mature counterparts.
The full study can be downloaded here (registration required).







