Trend Micro’s Cloud One Now Protects Apps with Runtime Security, Preemptive Protection
Trend Micro is expanding its cloud-native security offerings with pre-emptive protection for a wide range of modern apps – cloud, hybrid, serverless and APIs. IDN explores Cloud One – Application Security with vice president Wendy Moore.
by Vance McCarthy
Tags: APIs, app security, Cloud One, cloud-native, protection, security, serverless, Trend Micro,

vp, product marketing

"Whether building applications on-premises, as a container in the cloud, or using serverless designs, security tools shouldn’t interfere with the development pipeline."
Architecture Summit
 Enterprise-Grade Integration Across Cloud and On-Premise
Enterprise-Grade Integration Across Cloud and On-PremiseTrend Micro is expanding its cloud-native security offerings to protect modern apps – with support for on-prem, hybrid, cloud-native apps, serverless and APIs.
Trend Micro Cloud One – Application Security is designed to provide code-level visibility and protection against the latest cyber threats. It is delivered as part of the company’s Cloud One platform. The solution offers embedded security for runtime protection, which will help businesses ensure their data is protected in newly adopted environments, according to Wendy Moore, vice president of product marketing for Trend Micro.
Cloud One – Application Security also stops runtime attacks before they occur and helps developers pinpoint vulnerabilities in internally-developed or third-party code that the attack could exploit, she added.
This level of visibility will also help teams prioritize their response and take practical next steps to resolve app-centric security issues.
The release of Cloud One – Application Security comes as Gartner released a report that quantifies the rapid growth in modern app architectures. “More than 50% of global enterprises will have deployed serverless function platform as a service (fPaaS) by 2025, up from less than 20% today,” the report said in part.
“Whether building applications on-premises, as a container in the cloud, or using serverless designs, security tools shouldn’t interfere with the development pipeline. With Application Security, businesses can deploy advanced protection across legacy and modern frameworks and languages with ease,” Moore said,
The ‘Intelligence’ in Trend Micro’s Cloud One – Application Security
Trend Micro’s Cloud One – Application Security is also designed to lower app developers' barriers to work with security, Moore added. The solution will let developers “deploy security as code into applications in only two minutes with no additional code changes or rules to set up,” she said.
IDN asked Moore to detail more about how Trend Micro delivers app security ease-of-use.
“The deployment of Cloud One – Application Security is very easy,” Moore told IDN. “The application developer engineer will add the Cloud One Application Security library to the application code, but once you have done that, Trend Micro will instrument the application to protect its contents from hackers or malicious events. Because the instrumentation is automatic, application developers do not need to rewrite their code.”
With this approach, Trend Micro can protect home-grown code, as well as third-party libraries, Moore added. “While Cloud One - Application Security offers a wealth of default application security rules, we [also] allow customizations and exceptions of these rules,” she added. This approach to including default rules alongside the ability to customize “provides advanced runtime web application security, integrated where needed without impacting the speed and agility of development teams or requiring new skill sets for security practitioners,” Moore added.
Securing Modern Apps, Architectures – from Design-To-Deployment
Cloud One – Application Security also lets enterprise teams manage and secure a broad range of apps and architectures, including on-prem, cloud-native in popular public clouds, or cloud apps that use microservices across multiple clouds.
“We help maintain security of these environments with runtime visibility into threats, as well as code-level information when vulnerabilities are found,” Moore told IDN. Also, it supports apps written in many languages and across containers and serverless environments, such as AWS Fargate and AWS Lambda, she added.
Moore also explored how Cloud One – Application Security helps teams new to cloud-native apps' development/deployment. In particular, she explores how Trend Micro helps developers enact emerging best practices across design to deployment.
For those building cloud-native applications, your focus will be on containerized infrastructures with microservices architectures. Threats can surface across the entire application environment; however, many vulnerabilities start with the application build cycle, including open source code as well as the supporting container images. This can include malicious packages from public sources, as well as cross site scripting, or secrets and keys left in an image and detected by a hacker.
This is where Cloud One – Container Security comes in using container image scanning, as well as open source vulnerability detection powered by Snyk. Cloud One – Container Security container admission control policy also prevents container images from being run in production when they may present a risk.
This is done by adhering to policies and rules set by security teams to prevent or permit images from being allowed into production runtime environments. This can include checks to disallow images set as privileged containers, or that allow access to the root filesystem which can result in serious breaches.
Once the application is in production, Cloud One - Container Security container runtime protection will protect the application in the cluster from vulnerabilities such as Struts vulnerability, CVE-2017-9805, which was responsible for the Equifax data breach. Cloud One – Application Security protects the application itself from the inside, including embedded protection for APIs and help to protect against OWASP top 10 threats such as SQL injection, and remote command executions.
Recent research from Trend Micro Research identified the top threats targeting serverless apps, include theft of credentials, sensitive data and code.
These and all application-layer attacks are commonplace cybersecurity threats being leveraged against a new attack surface. Using Trend Micro’s Cloud One platform, teams can implement a range of security services and compliance checks alongside Application Security without hindering agile cloud development and deployment.
How Cloud One – Application Security Thwarts Threats to Modern Apps
Moore also shared how developers can use Cloud One – Application Security to thwart common application security threats.
“Organizations need to think about detecting weak misconfigurations in such infrastructure as web application firewalls to avoid customer credit card losses or identify compliance issues across your cloud service provider account,” Moore told IDN.
“Cloud One – App Security can protect against misconfigured Kubernetes environments and access management where network policies are not applied and can allow attackers access to move laterally within container pods and take control of containers. It also acts as a guardrail for best practices and immediate awareness of your cloud security gaps, as well as remediation needs for those that are coming from a traditional application space to cloud-native tools and platforms,” she added.
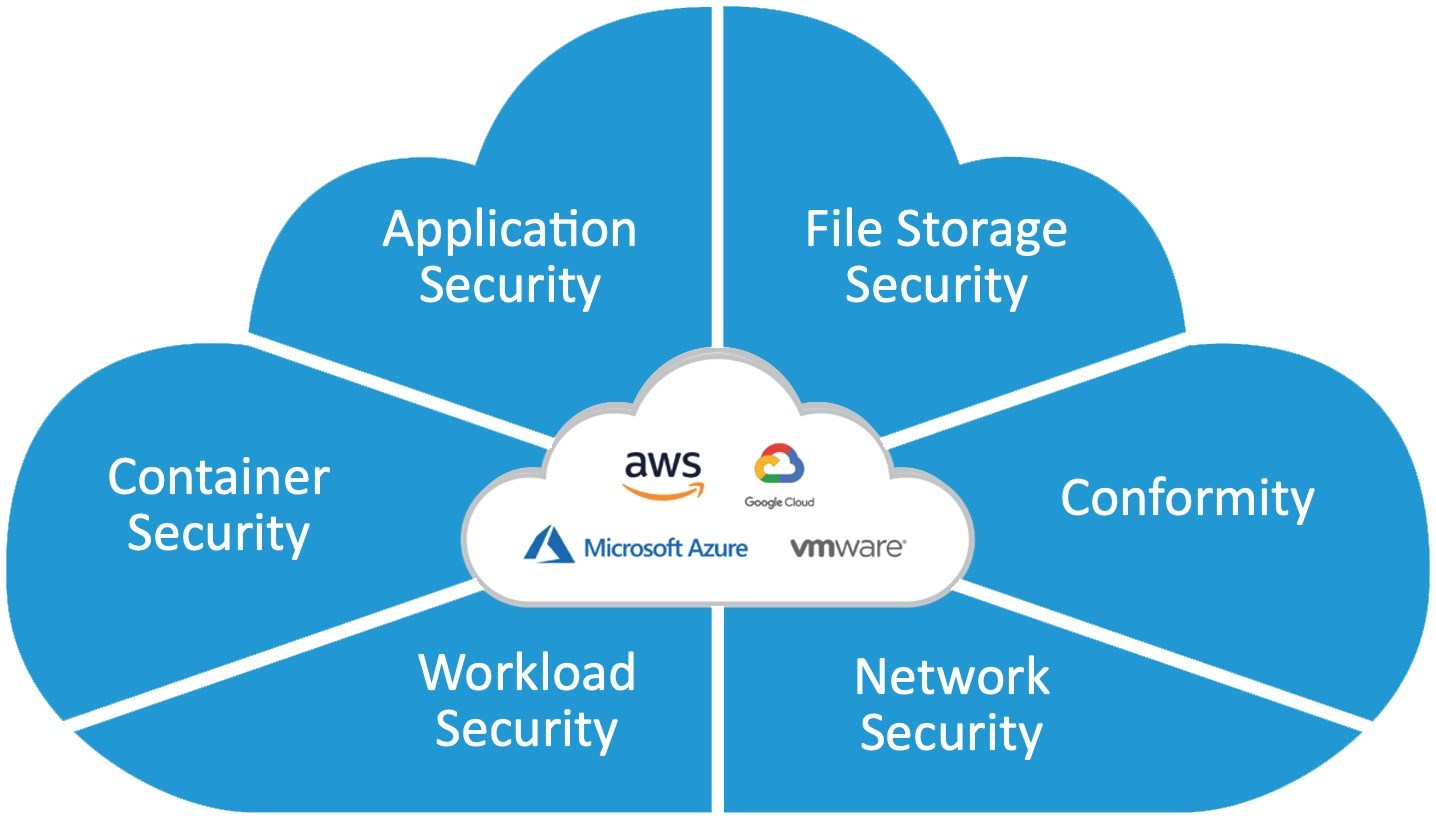
Trend Micro Cloud One – Application Security is part of the company’s overall Cloud One security platform for protecting apps from build time to runtime for your hybrid and multi-cloud security requirements. The complete solution includes:
Cloud One – Conformity: For cloud security and compliance posture management,
Cloud One – Workload Security: For runtime protection of workloads (virtual, physical, cloud, and containers),
Cloud One – Container Security: For container image scanning, container admission control policy and container runtime protection,
Cloud One – Network Security: For cloud network layer IPS security, and
Cloud One – File Storage Security: For cloud file and object storage services. Combined, these services provide a powerful platform to help simplify
Learn moreabout Trend Micro Cloud One – Application Securityhere.
Related:
- Mirantis Lens Pro Looks to Simplify Kubernetes, Boost Developer Productivity
- SentinelOne Expands DataSet Technologies for Container, Cloud-Native Security
- 2021 Was Worst Year Ever for Ransomware; Two-Thirds of Victims Paid Ransom
- OutSystems, SAP Partnership Leverages Low-Code for Novel Solutions, Migration
- Orca Security's Attack Path Analysis Improves Protection for Cloud-Naïve Apps
All rights reserved © 2025 Enterprise Integration News, Inc.


